- 4 Android banking trojan campaigns goal lots of of finance and social apps
- Malware hides icons, blocks elimination, and overlays fake banking login screens
- Stay display screen streaming lets attackers monitor exercise and seize authentication steps
Safety researchers have tracked 4 Android banking trojan campaigns that depend on deception, stealth, and disappearing app icons to keep hidden out of sight after set up.
Researchers at Zimperium say the campaigns, named RecruitRat, SaferRat, Astrinox, and Massiv, collectively focused greater than 800 banking, cryptocurrency, and social media apps.
The potential attain is huge as a result of many generally used apps have billions of downloads, though precise infections seemingly quantity within the hundreds of thousands moderately than billions.
Article continues beneath
More and more advanced set up methods
The researchers be aware the attackers rely closely on tricking customers, moderately than exploiting technical flaws alone. Victims are directed to fake web sites disguised as job portals, streaming providers, or software program downloads that appear professional at first look.
Some campaigns imitate recruitment platforms, pushing victims to obtain an app as a part of a supposed hiring course of, whereas others promise free entry to premium streaming content material. This leads customers to sideload malicious software program from unofficial sources.
Set up methods have grown more and more advanced, with many assaults utilizing multi-stage supply strategies that conceal the true malware payload inside one other file.
One tactic entails mimicking official replace screens, together with layouts resembling the Google Play interface, to decrease suspicion throughout set up.
As soon as energetic, the malware usually requests Accessibility permissions, permitting it to monitor actions, learn display screen content material, and grant itself extra privileges with out clear consumer data.
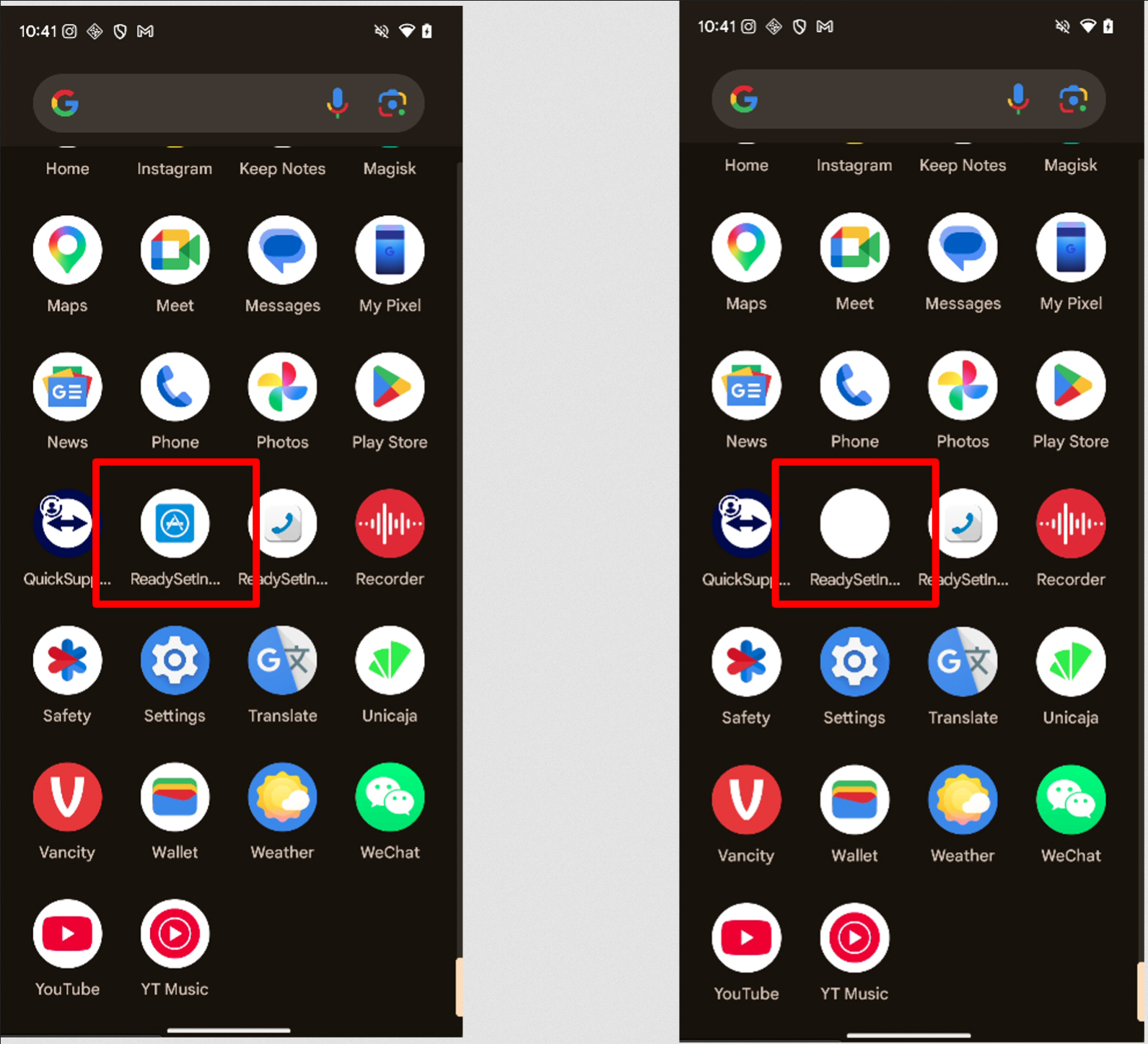
A very misleading characteristic permits sure variants to substitute their app icon with a blank picture, successfully making the app “vanish” from the system’s app drawer, creating confusion when customers try to find or take away the software program.
Different variations intrude straight with makes an attempt to uninstall the malware by redirecting customers away from system settings.
Display overlays play a significant position in credential theft throughout all 4 campaigns. Fake lock screens can seize PINs and patterns, whereas simulated banking login pages harvest credentials as customers work together with professional apps.
Some variants even show full-screen “replace” messages that stop regular interplay whereas background actions happen.
Past stealing credentials, a number of households transmit reside display screen content material to distant servers, making a steady visible feed that enables attackers to observe exercise and intercept authentication steps in actual time.
Encrypted communication channels join contaminated units to centralized command techniques that coordinate assaults and distribute up to date directions.
These techniques can handle hundreds of compromised units concurrently, making widespread financial theft simpler to arrange.
Zimperium’s researchers say evolving evasion strategies, together with hidden payloads and structural file tampering, make detection tougher for conventional safety instruments.

Observe TechRadar on Google Information and add us as a most well-liked supply to get our professional information, critiques, and opinion in your feeds.
Source link
#Android #malware #blank #icons #fake #screens #steal #financial #data