
Calvin Wankhede / Android Authority
TL;DR
- GrapheneOS has patched an Android 16 VPN flaw that Google reportedly determined to not repair.
- The bug might let a malicious app leak small quantities of knowledge outdoors an lively VPN tunnel.
- In excessive circumstances, which means it’s potential inventory Android customers might have their IP tackle leaked, even with strict lockdown controls enabled.
A VPN that may leak your location is a fairly large failure of the tech at the most effective of occasions, nevertheless it’s particularly regarding when Android’s lockdown controls exist to reassure you that it received’t occur. That’s the issue GrapheneOS has now addressed in Android 16, with a repair for a VPN flaw Google has reportedly determined to depart alone.
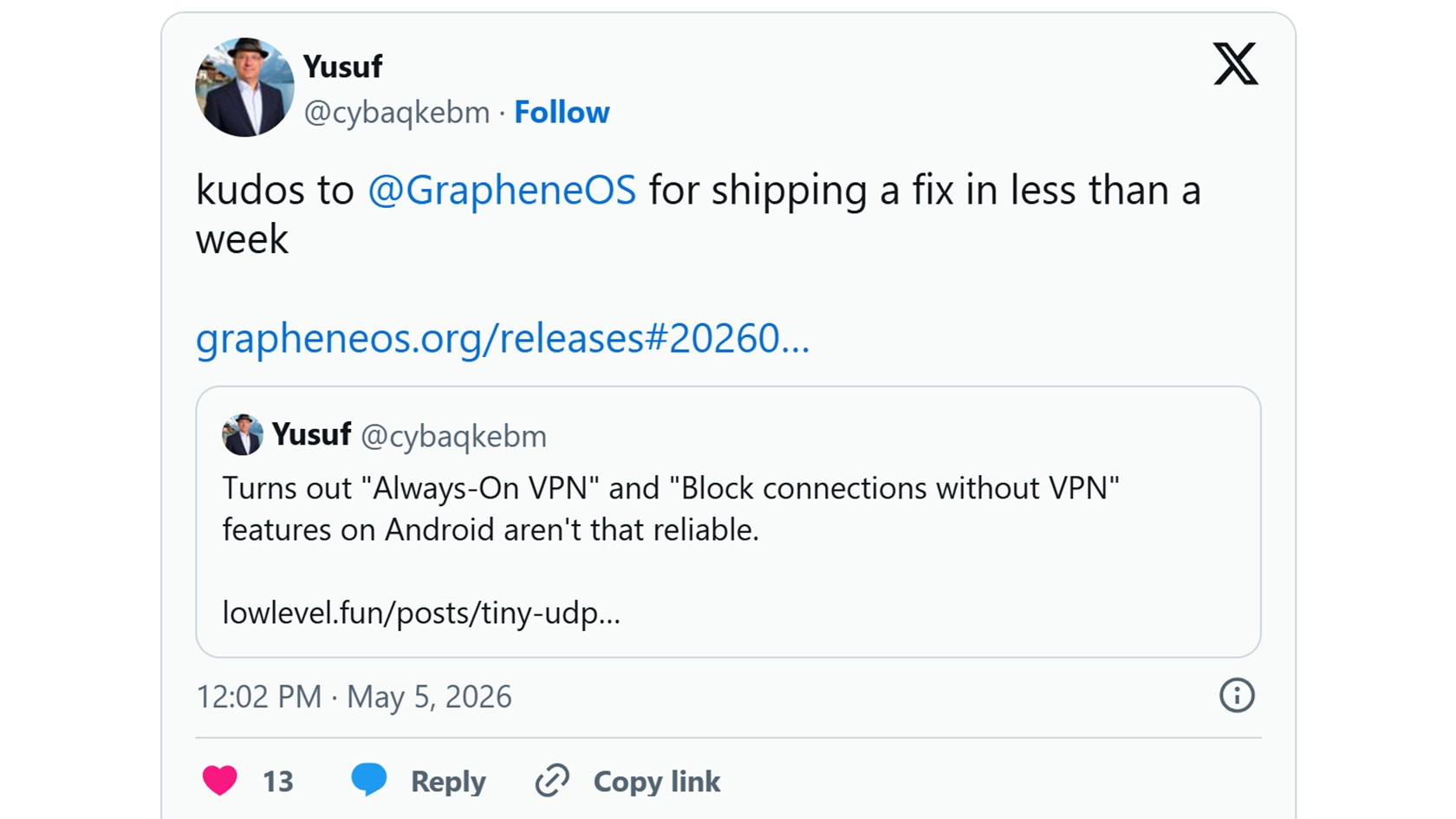
As reported by TechRadar, a safety researcher going by lowlevel/Yusuf not too long ago disclosed a bug nicknamed Tiny UDP Cannon. The problem impacts Android 16 and might enable a daily app to leak a small quantity of knowledge outdoors an lively VPN tunnel, doubtlessly exposing your actual IP tackle.
Whereas not a widespread threat, the most important crimson flag with the bug is that this may apparently occur even when Android’s strictest VPN settings are enabled. At all times-On VPN and Block connections with out VPN are supposed to stop visitors from leaving your cellphone except it goes by means of the VPN. They’re meant to provide you further peace of thoughts, however this bug creates a slim method round that safety.
Before you panic, it’s price noting that an attacker would want to get a malicious app onto your cellphone first to use this bug. That makes the day-to-day threat modest for many Android customers, nevertheless it’s nonetheless not superb should you depend on Android’s VPN lockdown mode as a critical privateness assure.
Don’t need to miss the most effective from Android Authority?


The flaw seems to stem from a networking optimization in Android 16. In accordance with the researcher, Android doesn’t correctly test whether or not a tiny packet of knowledge despatched whereas closing sure connections must be restricted by the VPN, so it may exit over the common connection as a substitute. If the malicious app ensures that the packet comprises your IP tackle, it undermines one of many largest causes that folks use VPNs within the first place.
Google’s Android Safety Group reportedly categorized the problem as “Gained’t Repair (Infeasible)” and determined it wouldn’t be included in a safety bulletin. GrapheneOS — the security-focused Android-based working system targeted on Pixels — took a unique route, disabling the underlying characteristic totally in launch 2026050400.
For GrapheneOS followers, it’s one other demonstration that the OS takes these privateness edge circumstances extra significantly than its rivals. Inventory Android customers don’t have a neat official repair proper now, although the researcher notes the characteristic will be turned off manually through an ADB command.
Thanks for being a part of our neighborhood. Learn our Remark Coverage before posting.
Source link
#GrapheneOS #closes #Android #VPN #loophole #Google




